A Blockchain solution
Problems facing traditional centralized social media & a decentralized solution
Traditional social media are subject to limitations including misinformation, censorship, privacy, political neutrality, user control, and malicious activities etc, due to its centralized nature. Hacking, user privacy threats, breaching of data rights etc are posing severe risks to users' proprietary rights, data privacy and data security. Data created during users' socializing process does have great values to be harnessed and applies in a more scientific way while centralized social media platforms failed in delivering it.
With Blockchain technology, we can return users' proprietary rights and profits back to them!
Decentralized social networks operate on independently run servers, rather than on a centralized server owned by a business. Blockchain technology allows data entries to be stored in servers anywhere in the world. It fosters transparency, as the data can be viewed in near real time by anyone on a network.
Decentralized social networks give users more control and autonomy. An individual can set up their social network and determine how it operates and what users can say. Instead of having content monitored by a corporation, the founder of a federated social network can establish the terms of acceptable behavior for the site.
Social media promotes connectivity, community building, and knowledge sharing. People can use social media to drive social and political change, bring awareness to important issues, raise funds for those in need, and promote their businesses. However, social media’s ugly side can include cyberbullying, political misinformation, and even criminal activity. Because decentralized social networks are largely unmoderated, both the positive and negative outcomes become more extreme.
User Control, Free Speech, and Censorship Resistance
Corporate entities control major social media sites, and a small group of people within these companies sets the rules of engagement. This has raised concerns about free speech and censorship among users. Last year, Facebook enacted high-profile bans on individuals from all sides of the political spectrum, from Louis Farrakhan to Alex Jones. Banning violent, hateful, and dangerous messaging helps protect social media users from malicious online activity, but some believe the bans run contrary to ideals of free speech.
A decentralized social network allows users more control. Unlike centralized social networking platforms, federated networks foster independence without a central authority. Benefits include censorship resistance, ownership over personal data, and improved control over user-generated content. In other words, users do not accept censorship and insist on having the final say on their content. This means no one else, whether a corporation or site administrator, can make modifications to content created by users. No one can remove content generated by users, either.
In a federated network, no single group can dictate other groups’ rules. For example, anyone on Mastodon can run their own social media site without a central authority, meaning they (and other users) can post anything they want without worrying about having their post taken down. A downside of this structure is that hate groups also have the freedom to launch their own social media sites. While individuals can block these groups, they cannot prevent them from engaging on the network.
Personal Data, Privacy, and Security
User concerns about control of their personal data have led to the establishment of the General Data Protection Regulation (GDPR) in Europe. The legislation considers users “data controllers.” Social media companies are known as “data processors.” The GDPR definition of data controller means that users own their own data. By law, companies must hand over more control of personal data to users, at least those based in Europe. Companies are penalized for not following GDPR regulations.
Decentralized social networks have provided another answer to data privacy and security. On federated social networks, users can create accounts without having to link to real-world identities, like email addresses or phone numbers. Furthermore, these networks often rely on public-key cryptography for account security, rather than relying on a single organization to protect user data.
While this can create advantages from a data security perspective, it also presents challenges. For example, bootstrapped federated social networks may shut down because of a lack of funds, causing users to lose their data and connections. In this instance, users have no simple way to reconnect with others on the network because federated networks do not keep records of personal data on servers. In terms of privacy, these platforms do not necessarily encrypt data, which means that private messages may be visible to administrators.
Economic Neutrality
Economic neutrality is an essential ideal for many who turn to decentralized social networks — they wish to liberate themselves from invasive advertising and the risk to privacy it poses. Federated networks look to new forms of monetization to remain solvent. They often use a form of digital currency, such as Bitcoin, to keep operations running. For example, Steem pays its users for creating or curating intriguing content, which incentivizes content creators to focus on quality. Steem gets its money from investors who believe the platform will grow in value over time and will one day be profitable.
Data becomes the No.1 Productivity Factor
Data is the lifeblood of the modern global economy. Digital trade and cross-border data flows are expected to continue to grow faster than the overall rate of global trade. Businesses use data to create value, and many can only maximize that value when data can flow freely across borders, yet a growing number of countries are enacting barriers that make it more expensive and time consuming, if not illegal, to transfer data overseas.
The reasons for the enacting barriers are risks being exposed during data use and transactions. In places where data can be accessed and shared, personal data breaches are more likely to occur. Such breaches will not only cause harm because of the privacy violation of the individuals whose personal data have been breached, but can also cause significant economic losses to the business affected, including loss of competitiveness and reputation.
Data security risks included: illegal data transactions, data breaches and thefts, violation of privacy and intellectual property rights, data tempering, data used in criminal activities etc. Aforesaid data security risks are due to the lack of administration and transparency during data production, transfer and sharing. By using Blockchain based technologies and privacy computing, myMessage will be able to fill the blanks missed in the whole process. Data can be immutable, temper-proof, verifiable and secure when people use myMessage’s Dapp for sending, reading, encrypting, searching of messages and data as well as the data marketplace for permissionless trading.
In a digitalized world, data becomes the most fundamental factor for productivity and economic growth. Data becomes the most valuable asset of all. When it comes to data storage, now people are more keen on using cloud online data storage services such as DropBox, Google etc.
Nowadays people are more accustomed to using cloud or online message and data services. However, the cloud services are subject to disadvantages and security risks, including but not limited to:
I. Certain Cyber-attack Vulnerabilities
One of the most obvious disadvantages of the cloud storage model that many businesses use is that that data isn’t under your own secure supervision. Depending on the cybersecurity architecture implementation of the public (or private), a cloud provider may be more vulnerable to certain varieties of cyber attacks that are specifically designed to penetrate the cloud. First, let’s take a look at how the cloud is set up from a cybersecurity standpoint, so you can better understand potential vulnerabilities.
Cloud services are also highly exposed to the following security breaches:
• Distributed Denial-of-Service (DDOS) Attacks
• Phishing & Social Engineering
• Common Provider Vulnerabilities
• etc.
II. Slower Backup & Restoration Times
When you’re working with data via an on-premise model, your data, machines, and servers are located closely nearby. Whether it’s in the next builder over, or in your home office, on-premise networks are often connected physically. When data moves through the cloud, however, you’re subject to internet bandwidth speeds and limitations. In the end, your internet bandwidth and maximum cloud provider speeds may end up being slower than if you were transmitting data on a local network.
This can result in communications latency issues, where it may take time for one user to view a file that another user has uploaded to the cloud in a different city, for instance. Where this can be the biggest disadvantage is in terms of backing up files and servers.
III. Risk of Extended Downtime
The third disadvantage to cloud storage is the risk of prolonged system downtime and is one of the downsides the most often cited by businesses. Simply put, the servers where your data exists aren’t in your office or building, they’re at Amazon, Google, or wherever your cloud provider has their server farms. Therefore, your internal IT staff isn’t in control of remediating systems issues and getting your networks back online.
IV. Third-Party Regulatory Compliance
Depending on the nature of your industry, there will likely be certain government and/or industry standard regulations that you’ll need to comply with in terms of your cloud service provider’s cyber defenses. In some very rare cases, you may be prohibited from using cloud storage altogether for extreme privacy and/or security concerns. Either way, bringing on a cloud partner for data storage entails being informed about the compliance issues in your industry, and ensuring that your provider is meeting them.
V. Vendor Lock-In
Selecting a cloud service provider is more like a long term marriage than dating. Especially for large organizations with tons of data, migrating everything into the cloud, configuring the system, and ensuring compliance can take months or even years.
Therefore, you’ll need to be very selective when searching for a cloud storage partner. Depending on the service you use, and the nature of the contract, you’ll likely be locked into that specific vendor for at least a year (or maybe more).
A Blockchain-based Solution
The blockchain is a peer-to-peer distributed ledger in which records called blocks are linked and secured using a cryptographic hash. By design, blockchains are decentralized, secure, immutable and extremely fault-tolerant, making them suitable for record management activities i.e., financial transactions, identity management, provenance and authentication. Blockchain can be deployed as permissionless (e.g., Bitcoin or Ethereum) or permissioned blockchain e.g., Hyperledger Project by The Linux Foundation. In permissionless or public blockchain the actors in the system are not known. Anyone can join or leave the blockchain network at any time, which may raise security risks in the network. However, in permissioned or private blockchain only known and identifiable sets of participants are explicitly admitted to the blockchain network. This reduces the presence of malicious actors within the network. As a result, only authenticated and authorized actors can participate in the network which increases the security of the system as required by the enterprise applications. The concept of permissioned blockchain is gaining a lot of interest especially for non-financial use cases (other than the cryptocurrencies) in which the users are authenticated and authorized to participate in the network.
Many people continue to wonder how they could store files, documents, pictures, or videos, permanently. Various techniques have been adopted by people to keep their precious files for generations to come. These techniques include the use of pen drives, SSD hard disk, cloud storage, and even multiple PCs as forms of storage. Moreover, people have also embraced the use of paper or hardcopy storage, CD, DVD, and many more.
“Moreover, people believe that storing copies of an original document at different distant locations may help solve the problem of loss of the original to threats such as theft, fire or earthquake. More so, some people feel most secure when their document is stored at three distant locations." [1]
It is true that information stored using the above techniques may last long, however, they tend to get misplaced or spoilt after a long time. Furthermore, a pen drive, SSD hard disk, physical storage, or DVD could get damaged, lost in transit, or stolen. More so, a proven fact is that “condensation from high temperatures or high humidity can lead to the shortening of circuit boards or corrosion of contacts.” [2]
“Recordable CD-RWs may seem to be durable and secure, and optimists have estimated that they could last for 20 to 30 years. However, real life experiences have proven otherwise as manufacturers began introducing discs of variable quality to the market, some of which would not endure up to a year.” [1]
What about cloud storage such as Dropbox, Google Cloud, Apple iCloud, and Microsoft Cloud? They may seem reliable but are very prone to hacking: It happened in the past, and it would happen in the future. Furthermore, your information stored in the cloud storage can be lost, modified, hacked, or deleted if it is inactive for years. Therefore, they cannot be classified as permanent storage. [3].
“However, the biggest cause of concern for Cloud storage is not hacked data, it is lost data. For instance, Dropbox recently had a glitch in their sync system, and it left many subscribers with lost files. For those who only had their files hosted on Dropbox, there was no possible way to retrieve them.” [4]
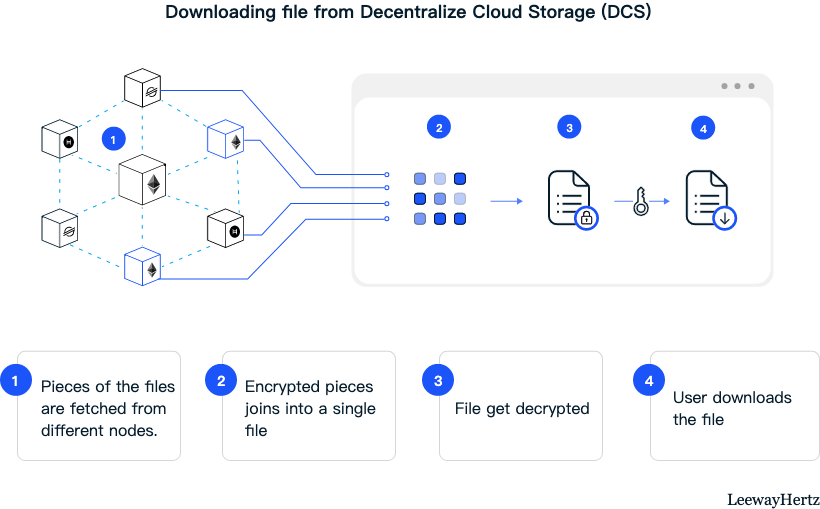
Because of this, this project aims to create a means of storing information permanently for decades at a low cost. The proposed storage technique for myMessage is the use of blockchain, which is immutable, undeletable, secure, and timestamped. With blockchain, you can store your information forever, and no one would be able to delete, modify, or steal your information. Moreover, if you want your information to be kept private, you can encrypt it, hence no one would be able to see your information without having the secret key.
Last updated